In this blog post, we introduce the recently published draft of the EU Cyber Resilience Act (CRA) which aims to substantially increase the cybersecurity of products sold in the European Union. Moreover, we discuss why the CRA regulations are especially costly to implement when products rely on open-source software.
The draft of the Cyber Resilience Act (CRA) presented by the European Commission is an important step towards strengthening the general cybersecurity of products sold in the EU. Especially for critical products, which are used e.g. in the industrial environment in the form of Industrial Automation & Control Systems (IACS) or Industrial Internet of Things (IIoT) devices, a higher protection against cyberattacks is long overdue. Past cyberattacks, e.g. the WannaCry ransomware (2017) or the software supply chain attacks on software from SolarWind (2021) or Kaseya (2021), impressively demonstrated that cyberattacks can cause economic damage in the billions.
In order to increase the cybersecurity of products, the CRA draft calls for a number of technical characteristics that regulated products must fulfill (see Annex I). In addition, the product manufacturer is required to take further steps during product development and subsequent product support, including conducting a cybersecurity risk assessment, performing due diligence when integrating third-party components, documenting relevant cybersecurity aspects, e.g., vulnerabilities that have become known, and implementing rules and procedures to disclose and address vulnerabilities (see chapter 2, article 10). Today, it is inevitable that the software running on those products is composed of in-house developments, purchased solutions from suppliers and open source software, e.g. in the form of software libraries, applications or operating systems. The CRA states very clearly that open source software itself is not covered by the regulation, in order to not hamper the publication of open source software (see page 15, paragraph 10). However, the CRA also states that the cybersecurity of open source software must be guaranteed by the product vendor when included into the product (see page 39, paragraph 4). Verifying all open source software components to prevent a cyberattacker from compromising the product will lead to a tremendous increase of the product development costs for the vendors.

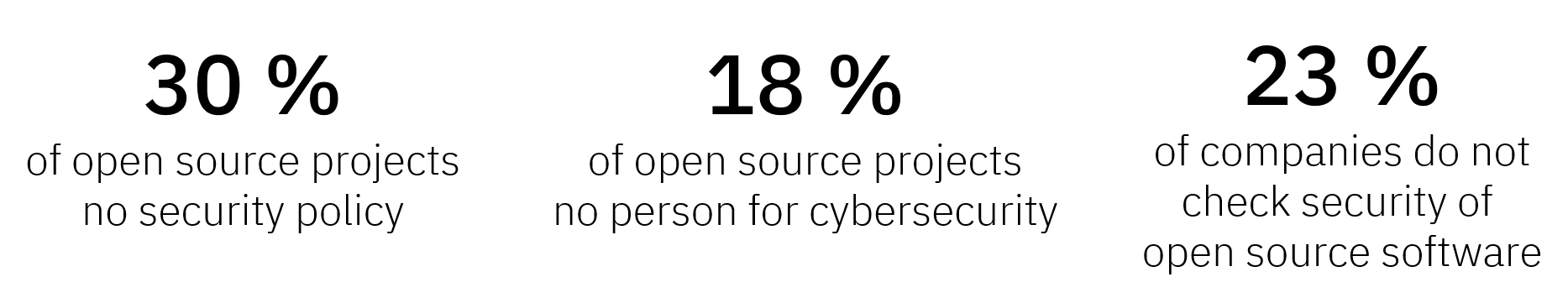
According to the Bitkom Open Source Monitor from 2021, 71% of the questioned companies stated that they use open source software, whereby 41% of those said that they also integrate open source software into their own products. The reasons why open source software is used are manifold, but the most important aspect is cost saving. From a research point-of-view. there is no clear evidence that open source software is in general more or less secure than software developed in-house. The cybersecurity of open source software depends on multiple factors like the financial situation of the open source project, or the experience and number of its developers. In a study performed by the CISPA research center in 2022, 30% of the questioned open source projects did not define a security policy and 18% did not define a person responsible for cybersecurity topics. This shows that a cybersecurity analysis of open source software is to be recommended. Unfortunately, the Bitkom Open Source Monitor revealed that 23% of the questioned companies do not check the security of the open source software they use.
The great danger of insecure open source components is that a cyberattacker can exploit vulnerabilities in the open source software to infiltrate the system and in the end compromise the complete product. In the case of open source software, handling these threats with the help of compliance processes, in which the responsibility for the correctness and maintenance of the software is handed over to the supplier, is of course not possible since the authors of the open source software cannot be held liable. Thus, very time and cost intensive cybersecurity analyses of the source code of open source software must be performed by the vendor in order to not endanger the security of the product.
The SANCTUARY Zero-Trust Platform tackles exactly the described challenge, where open source software is combined with third-party and in-house software on critical embedded devices. With its strong isolation features, the Zero-Trust Platform encapsulates software components and separates them from each other. As a result, a vulnerability in one software component which gets exploited by an cyberattacker will not negatively influence the security of the other software components. With regard to the EU Cyber Resilience Act (CRA), the SANCTUARY Zero-Trust Platform allows vendors to build products that fulfill the technical requirements of the CRA and at the same time to keep the development time of the products low since a less stringent security analysis is required to keep the entire product secure.
