Leverage our cybersecurity expertise to uncover the security weaknesses of your products and learn how to prevent them effectively.
Leverage our cybersecurity expertise to uncover the security weaknesses of your products and learn how to prevent them effectively.
Leverage our cybersecurity expertise to make your products ready for upcoming regulations like the EU Cyber Resilience Act.
Leverage our cybersecurity expertise to make your products ready for upcoming regulations like the EU Cyber Resilience Act.
The required security level of an embedded product depends on many factors.
Combine our security portfolio with customized solutions to build embedded products with rock-solid security that exactly fit your needs.
The required security level of an embedded product depends on many factors.
Combine our security portfolio with customized solutions to build embedded products with rock-solid security that exactly fit your needs.
Beyond Systems.
At SANCTUARY, we pioneer proactive security solutions tailored for a broad range of industries, including manufacturing, space, and automotive. Our expertise lies in creating advanced, next-generation security solutions that effectively protect embedded systems from emerging cyber threats.
Insight
Effortless OT Asset Management.
SANCTUARY Insight delivers a one-stop solution, effortlessly automating OT asset management, vulnerability analysis, and actionable recommendations. Effortlessly identify every device, from network equipment to field sensors, and achieve detailed insights through native protocol communication, all while ensuring zero disruption to your critical operations. Take back control of your OT today.
Zero-Trust Platform
Ultimate Protection for Embedded.
Discover the SANCTUARY Zero-Trust Platform: the ultimate software solution engineered to fortify your embedded products against the most sophisticated cyber threats. Leveraging cutting-edge virtualization technologies alongside trusted computing’s robust security guarantees, our platform ensures unparalleled isolation of third-party and open-source software.
News: Stay informed
- News
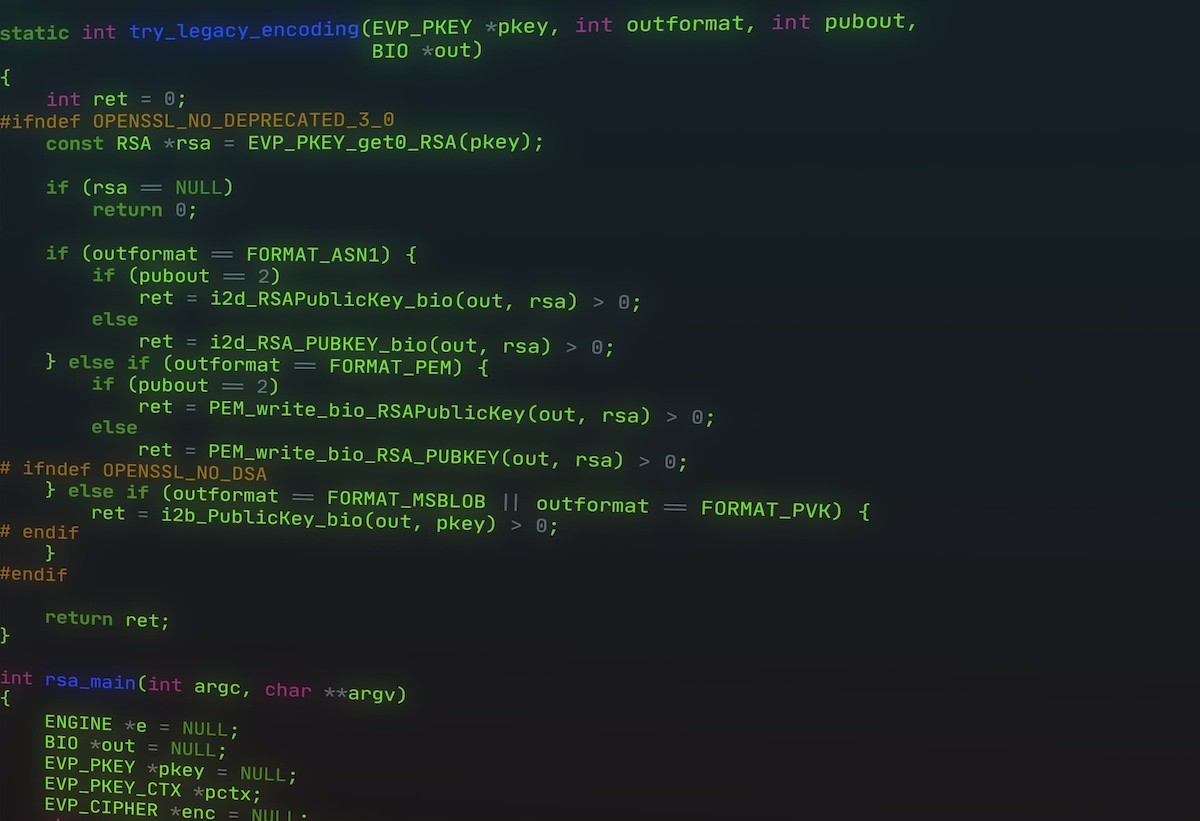
Stack Overflow in wolfTPM RSA Key Export Discovered
The SANCTUARY team uncovered a stack‑based buffer overflow in wolfTPM’s wolfTPM2_RsaKey_TpmToWolf function.

- News
End-To-End Supply Chain Protection for Satellites
SANCTUARY Wins ESA Tender for Developing Solutions for Securing Software Supply Chains of Satellites.

- News
Advanced Security and Recovery Mechanisms for Spacecraft
SANCTUARY Wins ESA Tender for Developing Solutions for Detection of Unauthorized Access and Control Restoration of a Spacecraft.

- News
Trusted Platform Module as a Service for Satellites
SANCTUARY Secures ESA Tender for Creating a TPM-as-a-Service Solution.
- News
Next-Generation Public Key Infrastructure for Space
SANCTUARY Secures ESA Tender for Developing Space-Specific Public Key Infrastructure.

- Event
Join SANCTUARY at Space Tech Expo Europe and SPS Trade Fair: Innovating Cybersecurity in Space and Beyond
Join us at SANCTUARY as we showcase our cutting-edge cybersecurity solutions at Space Tech Expo Europe and the SPS trade fair from November 14th to 16th. Discover how our expertise in advanced security architectures and software protection is pioneering safety in space and industrial automation.

- Event, Publication, Use Cases
Hardware-Based Isolation for Advanced Safety and Security in Spacecraft
Our team presented a paper on the research prototype of our Zero-Trust Platform for spacecraft, which secures mission-critical flight-control software in space, at the SpaceOps 2023 conference in Dubai. We also attended a spacecraft digitalization conference in Germany, connecting with industry leaders and staying up-to-date on the latest advancements.

- Event
Visit Us at embedded world 2023!
Exciting news! We’re thrilled to announce that we’ll showcase our latest technological innovations and solutions at the start-up@embedded world booth (3A-325e) at embedded world 2023, which will take place from March 14th to 16th in Nuremberg, Germany.

- Know-how
Hypervisor-assisted Debugging
Debugging options are often quite restricted when porting low-level software to an embedded device. Serial output and printing do not work, so what’s next? In this blog post, we go through typical problems and hypervisor-assisted debugging as a potential alternative.

- Event
Workshop at escar Europe 2022
On 15.11.2022, we held a workshop on Trusted Computing at the escar Europe conference. In particular, the workshop focused on the requirements of Trusted Computing in automotive scenarios.

- News
On the Upcoming EU Cyber Resilience Act
In this blog post, we introduce the recently published draft of the EU Cyber Resilience Act (CRA) which aims to substantially increase the cybersecurity of products sold in the European Union. Moreover, we discuss why the CRA regulations are especially costly to implement when products rely on open-source software.
- Know-how
Managing Run-Time Vulnerabilities
Run-time vulnerabilities are a nasty problem of modern software engineering. In this post, we examine a number of approaches that have been proposed and implemented by the security community. Some approaches aim at preventing the existence of bugs, some others aim at finding the bugs before the code is deployed, and yet others aim at making existing bugs harder to exploit in the field.
- Know-how
Webinar on Trusted Computing Technologies
SANCTUARY is proud to introduce its first free webinar on the basic concepts of Trusted Computing and which threats Trusted Execution Environments have to sustain.
- News
On the New German Cybersecurity Agenda
The German BMI’s recently unveiled cybersecurity agenda calls for broadly promoting innovation, increasing risk awareness, and responding more quickly to cyber threats through closer ties with government agencies. However, these measures are too reactive.
- Use Cases
Continuous Protection in Industry 4.0 with Sanctuary
In this blog post, we discuss the need for suitable security solutions in the context of smart industries and show how Sanctuary can support companies to enable the full potential of the fourth industrial revolution.

- Know-how, Publication
Trusted Container Extensions for Container-based Confidential Computing
In this blog post, we introduce Trusted Container Extensions (TCX), a novel container security architecture we designed as part of our applied security research efforts.

- Know-how, Publication
SafeTEE: Combining Safety and Security on ARM-based Microcontrollers
We are proud to announce that our paper on SafeTEE, a novel safety and security architecture for ARM-based microcontrollers, got accepted at DATE 2022!

- Event
Confidential Edge Computing @ Horizon Cloud Summit
We just gave a talk about applying lessons learned from Confidential Cloud Computing to the Edge at the Horizon Cloud Summit 2021.

- Know-how
Security Services: Secure Boot
Secure Boot is one of the powerful security services offered by Sanctuary, which can protect systems from rootkits and another advanced persistent threat (APT). This article explains the concept of secure boot and discusses different aspects of this technology.

- Know-how, Publication
Security Architectures on the open RISC-V Platform
Our systematization of knowledge publication „In Hardware We Trust? From TPM to Enclave Computing on RISC-V“ which discusses RISC-V security architectures is published at the VLSI-SoC 2021 conference!
Collaboration Partners & Associations